Concept explainers
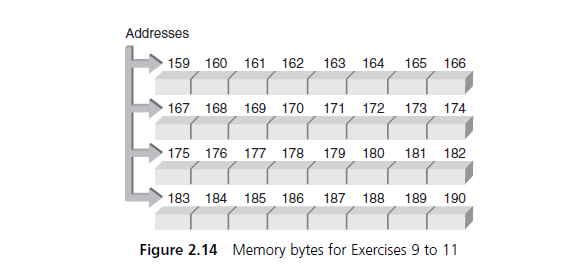
(Practice) a. Using Figure 2.14 and assuming the variable name rate is assigned to the byte at memory address 159, determine the addresses corresponding to each variable declared in the following statements. Also, fill in the correct number of bytes with the initialization data included in the declaration statements. (Use letters for the characters, not the computer codes that would actually be stored.)
b. Repeat Exercise 9a, but substitute the actual byte patterns that a computer using the ASCII code would use to store characters in the variables ch1, ch2, ch3, and ch4. (Hint: Use Appendix B.)
Want to see the full answer?
Check out a sample textbook solution
Chapter 2 Solutions
C++ for Engineers and Scientists
- (C PROGRAMMING ONLY) 3. How Much Is The House?by CodeChum Admin There's this house I want to buy just right around the corner. I know its address but I don't know its value. Can you please help me determine it? Instructions: In the code editor, you are provided with an initial code which has main() function.In the main(), the user is asked for an integer input and then its address is assigned to a pointer variable (see line 9)Your task is to print the value of the pointer variable using the dereferencing operator.Input 1. An integer Output Enter n: 5Value of *ptr = 5arrow_forward(b) For the following C statement, write the corresponding LEGV8 assembly code. Assume that the variables f, g, h, i, and j are assigned to registers X0.X1,X2,X3, and X4, respectively. Assume that the base address of the arrays A and B are in registers X6 and X7, respectively. B[3] = A[il + Alil:arrow_forward(Q4) Write a paragraph essay about the history of computer hardware and OS (Operating System). (a total of 25-30 sentences, or 1 and a half pages in length) Your essay must showcase your knowledge of hardware and software (PLEASE APPLY WHAT WE HAVE LEARN IN MS-WORD).arrow_forward
- 1. (Floating-Point Arithmetic). For each of the following numbers,(a) determine whether the number is a 4-digit oating-point number (the number of the FPA4);(b) if yes, write the number in the standard form ±0.d1d2d3d4 × 10n, where d1 is a nonzero digit and n ∈ Z;(c) if no, rst chop and then round the number to a number of the FPA4, written in the standard form:(i) − 0.989067000000001; (ii) − 51.8; (iii) − 900.377050000001; (iv) − 5000.0;(v) − 0.023409; (vi) 2036.0; (vii) 0.01814.arrow_forward1. (Assembly Language Programming) Write a procedure gcd for finding the greatest common divisor (GCD) of two positive integers x and y, which is described in the C code below. int gcd (int x, int y) { if (y 0) == return x; else return gcd (y, x % y); } Assume that x and y are passed to procedure gcd via X4 and X5 and the result is returned in X2. Note that x % y is the remainder of x / y.arrow_forward[1] ( Show your work. Show hoe you compute memory address by using the effective memory address computation. Assume the following values are stored at the indicated memory addresses and registers: Address Value 0x100 OxFF 0x104 OxAB 0x108 0x13 0x10c 0x11 $0x108 (Zrax) Fill in the following table showing the values for the indicated operands: Operand Value Zrax 0x104 4(%rax) 9(%rax, Xrdx) Register Zrax Zrcx %rdx 260(Xrcx,Xrdx) OxFC(Zrcx, 4) (Zrax, Xrdx, 4) Value 0x100 0x1 0x3arrow_forward
- (emu8086) Code in Assembly Create a programme which displays any four ASCII characters in ascending order.arrow_forwardc. (3 Pts) In a certain computer architecture, the content of some registers and memory content currently is as follows. Memory Address Data R1 | 00000004 0000FFFE FO00128A R2 0000FFFE FO00128A 0000FFF0 Next, this computer execute the following instruction. ADDI (0000FFFE), R1 Note: The I in ADDI refers to Indirect. Indirect here deals with the destination address: (0000FFFE). The parentheses are standard for indirect addressing. ADDI means add content of source to content of destination and place result in destination. Given that it is immediately after the instruction above is executed, fill out the contents of registers and memory addresses below. Memory Address Data R1 0000FFFE R2 FO00128Aarrow_forward)Choose the statement which is incorrect with respect to dynamic memory allocation.a. Memory is allocated in a less structured area of memory, known as heapb. Used for unpredictable memory requirementsc. Execution of the program is faster than that of static memory allocationd. Allocated memory can be changed during the run time of the program based on the requirement of the programarrow_forward
- (c) An electronic rainfall depth measurement device is developed to collect the data from the past 7 days as shown in Table 1 to study the weather condition at UniMAP. Table 1 [Jadual 1] Location: UniMAP Day Rainfall Depth (mm) 5.9 1 2 6.7 3 2.4 7.8 5.2 4 5 1.8 7 3.5 (i) Write a program in C to receive the values of rainfall depth and display the number of days with light rain ( 7.6 mm) from the record in Table 1. (ii) Rewrite the program in (c)(i) to identify and display the day with the lowest value of rainfall depth, the day with the highest value of rainfall depth and the average value of rainfall depth for the past 7 days.arrow_forwardProblem 4. (Decryption Program) Write a program called decrypt.py that accepts the private-key n (int) and d (int) as command-line arguments and a message to decrypt (produced by encrypt.py) from standard input, decrypts each character (represented as a fixed-width binary sequence) in the message, and writes the decrypted character to standard output. >- "/workspace/project4 $ python3 decrypt.py 3599 2839 000110000000010011010100001010100011001010100011001110000110010111100100 Cs110 $ python3 encrypt.py 3599 1759 | python3 decrypt.py 3599 2839 Python is the mother of all languages. Python is the mother of all languages. Directions: • Accept private-key n (int) and d (int) as command-line arguments. • Get the number of bits per character (call it width). • Accept message (binary string generated by encrypt.py) from standard input. • Assuming l is the length of message, for i E [0,l – 1) and in increments of width: Set s to substring of message from i to i + width (exclusive). Set y to…arrow_forward(System Architecture) One type of authentication is biometric using fingerprint. An Automated Teller Machine (ATM) requires fingerprint instead of PIN on top of the bank card. A user’s card must be registered with the user’s account number (10 digit), name, NRIC (12-digit) and three fingerprint samples of data type bitmap object. For a successful authentication, the correct bank-card provides the user’s account number to the ATM during read. The ATM retrieves fingerprint samples from a remote database. Then, the ATM requests the user to scan his right thumb finger print on an optical scanner. The algorithm authenticates the finger print against any of the three samples. A successful login requires a match of 99% on any one of the three samples. Question: Propose a class diagram. Draw a sequence diagram to illustrate the above sequence of process. Draw a wireframe design of the ATM User Interface (UI).arrow_forward
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education





