(BitOutputStream) Implement a class named BitOutputStream, as shown in Figure 17.22, for writing bits to an output stream. The writeBit (char bit) method stores the bit in a byte variable. When you create a BitOutputStream, the byte is empty. After invoking writeBit(‘1’), the byte becomes 00000001. After invoking writeBit (“0101”), the byte becomes 00010101. The first three bits are not filled yet. When a byte is full, it is sent to the output stream. Now the byte is reset to empty. You must close the stream by invoking the close() method. If the byte is neither empty nor full, the close() method first fills the zeros to make a full 8 bits in the byte and then outputs the byte and closes the stream. For a hint, see
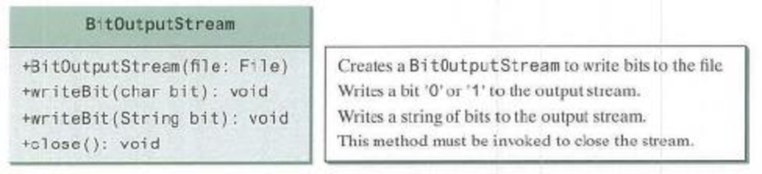
FIGURE 17.22 BitOutputStream outputs a stream of bits to a file.
Want to see the full answer?
Check out a sample textbook solution
Chapter 17 Solutions
Introduction to Java Programming and Data Structures, Comprehensive Version (11th Edition)
Additional Engineering Textbook Solutions
Differential Equations: Computing and Modeling (5th Edition), Edwards, Penney & Calvis
Modern Database Management (12th Edition)
Concepts of Programming Languages (11th Edition)
Starting Out with C++: Early Objects
Web Development and Design Foundations with HTML5 (9th Edition) (What's New in Computer Science)
Introduction To Programming Using Visual Basic (11th Edition)
- 2. [summary_report.py] Timesheet data is easy to represent in a file, where it can be used to generate a report and help the worker get paid! Given an example set of data where each row represents a day of the week and each entry on the row represents a block of time worked, like this: 1.5h 3.25h 3.8h 6.Oh 1.eh 5. 5h 2.25h 0.75h 2.25h 3.0h 3.0h 5.75h 2.25h A report could be produced by a program like this: 0.00h | 5.25h | 1.5en 3.25h 0.5eh 10.00h 0.00h 3.00h 6.00h 1.00h 8.50h 5.50h 2.25h 8.75h 8.25h 8.00h 0.00h | e.00h 2.25h 3.00h 3.00h 5.75h 2.25h Weekly Total: 40.00h Notice how in the output file all the numbers are nicely formatted as right-aligned. Hint: you will probably need to use splitting, string slicing, converting data types, and string formatting. create a program that uses a data file that you have created, parses the data in that file to create a calculation per row and a running total, then writes the report to an output file. Your program should prompt a user to input a…arrow_forwardThis is phython not Java Lab: Write a file copying program. The program asks for the name of the file to copy from (source file) and the name of the file to copy to (destination file). The program opens the source file for reading and the destination file for writing. As the program reads each line from the source file and it writes the line to the destination file. When every line from the source file has been written to the destination file, it close both files and print “Copy is successful.” In the sample run, “add.py” is the source file and “add-copy.py” is the destination file. Note that both “add-copy.py” is identical to “add.py” because “add-copy.py” is a copy of “add.py”. Sample run: Enter file to copy from: add.py Enter file to copy to : add-copy.py Copy is successful. Source file: add.py print("This program adds two numbers") a = int(input("Enter first number: ")) b = int(input("Enter second number: ")) print(f"{a} + {b} = {a+b}") Destination…arrow_forward<<Write in Java>> - Challenge 7 File encryption is the science of writing the contents of a file in a secret code. Your encryption program should work like a filter, reading the contents of one file, modifying the data into a code, and then writing the coded contents out to a second file. The second file will be a version of the first file, but written in a secret code. Although there are complex encryption techniques, you should come up with a simple one of your own. For example, you could read the first file one character at a time, and add 10 to the character code of each character before it is written to the second file. - Challenge 8 Write a program that decrypts the file produced by the program in Programming Challenge 7. The decryption program should read the contents of the coded file, restore the data to its original state, and write it to another filearrow_forward
- Did I correctly do this function? Did I correctly do the precondition and postcondition? //Precondition: flag_position is a non-negative integer and hBit_flags is a handle to a valid Bit_flags object.//Postcondition: returns the value of the flag at index flag_position if it is in bounds or -1 otherwise.int bit_flags_check_flag(BIT_FLAGS hBit_flags, int flag_position){Bit_flags* pBit_flags = (Bit_flags*)hBit_flags;int i = flag_position / 32;flag_position %= 32;return ((1 << flag_position) & (pBit_flags->data[i])) != 0;if (flag_position <= pBit_flags->capacity) { return *pBit_flags->data;}else{ return -1;}}arrow_forward9. to read data from data reader (dr1) just one time,, we write the following statement:- dr1.read(1) dr1.read() dr1.executereader nonearrow_forwardNetworking, TCP/IP requires one computer to function as the server and another to function as the client. The two computers must communicate using the same “language”. You will be building the server and the client. Write the program in C The Server Must accept commands in the form: PUSH “filename” fileSize <<<bytes>>> PUSH means that the client will be sending you a file. You need to store it with the filename sent. You must expect and require fileSize bytes. Respond to the client with “OK”. PULL “filename” PULL means that the client wants this file back. Respond with the number of bytes (use stat()), and then send all of the bytes to the client. Then respond with “OK” (a different send()). The server should take two parameters – the directory to work in and the port. The server should not shutdown. The server must have an accept() loop to allow multiple clients to connect (one at a time).arrow_forward
- This is Python Program 5: Improve the file copy program from Lab 9 so that it will make sure the user enters a file that exists. If a file doesn’t exist, the open function will raise the FileNotFoundError. You do not need to check if the destination exists since a file doesn’t need to exist to write it. Instead of copying the content of the source as exact, it only copies non-empty lines and it also prepend each line with a line number. A line is empty if the length of the line stripped of white space from both end is 0. The code segment below shows how to strip white space and getting the length of the string. If the length of the line is zero, the line is a blank line. line1 = " " line2 = " aa " print(len(line1.strip())) # 0 print(len(line2.strip())) # 2 In the sample run, “add.py” is the source file and “add-copy.py” is the destination file. Note that “add-copy.py” contains only non-blank lines from “add.py” and each line in “add-copy.py” is labelled with a line number. Sample run:…arrow_forwardPlease design the mapper and reducer for the below WordCount problem. WordCount problem: Given an input text file, count the frequency of each word in the file. Please design the input and output pairs for the Mapper and Reducer, use below table for reference. Input Output We get the "WordCount.jar" file by using the above table. It only contains Mapper and Reducer. There is no Combiner and no Partitioner in this program. Please illustrate how the WordCount.jar program works on the below dataset. This text file only contains one line. Dataset: the sound sounds sound. it is the right right, right? Suppose we run the WordCount.jar program on this file. Suppose that the space symbol, and "?" are all used for separating the words. The outputs of the Mapper are Mapper The outputs of the reducer are Reducer Answer: Are the results sorted alphabetically? When was it sorted? 2 27 20 35arrow_forwardWrite example of C++ program that reads and writes a binary file to a text file. It also prints the values accordingly to the consolearrow_forward
- It is necessary to specify the I stream's functionalities.arrow_forwardFile Stream Problem: Implement a Caesar cipher that can encrypt and decrypt text and file. A Caesar cipher is a substitution cipher that shifts the letters in the original message x spaces ascending the alphabet where x is the key. Example if the key for the cipher is 3, and the message is “I will be there.” Then the coded message would be “L zloo eh wkhuh” Program requirements: Create a class call CCipher that has two member functions encrypt and decrypt. The program should be able to encrypt/decrypt a message from a file as well as a keyboard input. The default key should be 3. The user should be able to select between encrypting and decrypting and should be allowed to do so multiple times until s/he decides to end the program. The file format to be encrypted should be a “.txt” and the user should be able to provide the name of the file to be encrypted, after which the file should be deleted. The user should have the option to view…arrow_forwardModify pipe4.cpp so that it accepts a message from the keyboard and sends it to pipe5. //pipe4.cpp (data producer) #include <unistd.h> #include <stdlib.h> #include <stdio.h> #include <string.h> int main() { int data_processed; int file_pipes[2]; const char some_data[] = "123"; char buffer[BUFSIZ + 1]; pid_t fork_result; memset(buffer, '\0', sizeof(buffer)); if (pipe(file_pipes) == 0) { //creates pipe fork_result = fork(); if (fork_result == (pid_t)-1) { //fork fails fprintf(stderr, "Fork failure"); exit(EXIT_FAILURE); } if (fork_result == 0) { //child sprintf(buffer, "%d", file_pipes[0]); (void)execl("pipe5", "pipe5", buffer, (char *)0); exit(EXIT_FAILURE); } else { //parent data_processed = write(file_pipes[1], some_data, strlen(some_data));…arrow_forward
 Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education
Database System ConceptsComputer ScienceISBN:9780078022159Author:Abraham Silberschatz Professor, Henry F. Korth, S. SudarshanPublisher:McGraw-Hill Education Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON
Starting Out with Python (4th Edition)Computer ScienceISBN:9780134444321Author:Tony GaddisPublisher:PEARSON Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON
Digital Fundamentals (11th Edition)Computer ScienceISBN:9780132737968Author:Thomas L. FloydPublisher:PEARSON C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON
C How to Program (8th Edition)Computer ScienceISBN:9780133976892Author:Paul J. Deitel, Harvey DeitelPublisher:PEARSON Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning
Database Systems: Design, Implementation, & Manag...Computer ScienceISBN:9781337627900Author:Carlos Coronel, Steven MorrisPublisher:Cengage Learning Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education
Programmable Logic ControllersComputer ScienceISBN:9780073373843Author:Frank D. PetruzellaPublisher:McGraw-Hill Education





