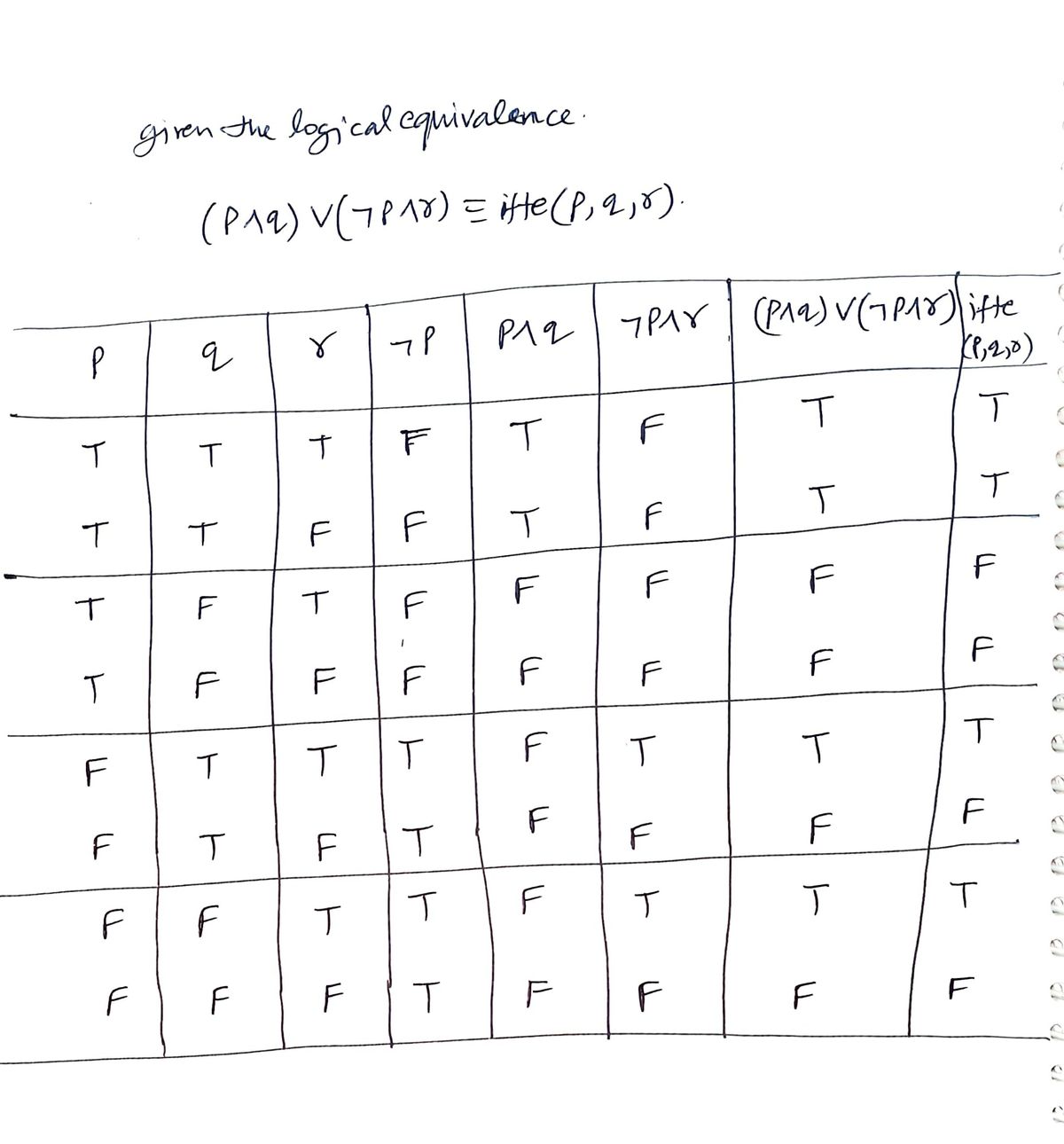
Show the following equivalence via truth table: (pA g) V (¬p r) = ifte(p, q, r)
Q: Directions: Create a timeline on the history of computers by filling out the needed information on t...
A: The inventor of the GUI (software program): Alan Page, Donald Tesler, Dan Parsons, David Watson, Wil...
Q: the longest sequence of increasing numbers. Use the function: void longestSeq
A: Below the C program for the longest sequence of increasing numbers
Q: Hi in the below code I would like to remove the blank tokens and how to achieve it. #include #i...
A: You want to remove blank token from your code.. So, In Strep 1 your given code and output. In step 2...
Q: is the process of transforming data from cleartext into ciphertext. Content Filtering Algorithms ...
A: ENCRYPTION : Encryption is a method to secure and protect sensitive digital data by means of advance...
Q: FIND THE FOLLOWING: e. time constant f. rise time g. settling time
A: First, let's understand what is time constant, Rise time and Settling time briefly Time constant ...
Q: write implementation of the pop() method for the well developed (using exceptions) StackADT I U + v ...
A: The solution to the given problem is below.
Q: Review the default firewall configuration ($ sudo iptables -L-n) and answer questions a. -C. Q1. Wha...
A: by bartleby guidelines i am able to do only one answer.
Q: Session Hijacking attacks are explained, as well as how users can protect themselves. Discuss potent...
A: Introduction: Session hijacking, sometimes referred to as TCP session hijacking, is a technique for ...
Q: 1. The input integer, n Constraints The value is >= 1 Output The first line will contain a message p...
A: Algorithm: Include standard header file and namespace std. Create a main function Declare the vari...
Q: F(A,B,C)= (A+B+C)(A+B+C)?
A: Logic Gates are used as building blocks in the digital system. It is an electric circuit which is ha...
Q: In order to ensure the confidentiality and integrity of financial information and recordkeeping in a...
A: Introduction: Since this is a discussion about SOX compliance, IT security controls must be in place...
Q: epresent the following decimal numbers in binary using 8-bit signed magnitude, one's omplement and t...
A: Here in this question we have given four decimal number and we have asked to find thier sign magnitu...
Q: Describe the tactics used to hijack a session. How can you defend yourself against such an attack
A: Given To know about the tactics used to hijack a session and defend yourself against such ab attack
Q: PYTHON Suppose you are taking out a bank loan. The bank charges 10% interest each year. How much do...
A: total_amount=principal+simple_interest total_amount=P+Ptr where r=R/100 ...
Q: ) In the second part you have to find or build a 2D grayscale image and write your own laplacian fil...
A: Laplacian Filter (otherwise called Laplacian over Gaussian Filter (LoG)), in , is a utilized in the ...
Q: Determine the difference between a virtual machine and a virtual machine.
A: The answer of this question is as follows:
Q: Write a program to create a file named Exercise1.dat if it does not exist. Append new data to it if ...
A: Write a program to create a file named Exercise1.dat if it does not exist. Append new data to it if ...
Q: (Java) Identify and correct the mistakes in the below program: public abstract class Dog { ...
A: NOTE: Code run successfully as above problem describe and Please follow my screenshot provided in b...
Q: a class, Team.java, that has the following: * two private instance variables: a String named color ...
A: // Java Code: import java.io.*; class Team{ //declaring the private variables private String color; ...
Q: build a simple graphical application that is responsive and that uses basic widgets and demonstrates...
A: the answer is given below:-
Q: Recall the naïve divide and conquer O(n2)-time multiplication algorithm, call it NaiveD&Cmult, to mu...
A: Answer: I have done code and also I have attached code and code screenshot as well as output
Q: Explain the difference between an application programming interface (API) and an application binary ...
A: API Full Form : Application programming interface ABI Full Form : Application Binary Interface The...
Q: Session Hijacking attacks are explained, as well as how users can protect themselves. Discuss potent...
A: Session hijacking is a type of cross-site scripting (XSS) attack that exploits vulnerabilities in we...
Q: Consider the below commands i) sed "s/CSH/csh/g" temp >|Is ~/newtemp 11) Is -v grep wc -1 111) Is -a...
A: Some operating systems used need commands to execute the functions unlike the operating system used ...
Q: What is the best way to get started with github?
A: Github is a platform where most of the developers in the world share there ideas, there project work...
Q: Assuming that the attacker has acquired the system's password database, this type of attack uses a d...
A: A rainbow table attack is defined as a type of hacking where the attacker tries to use a rainbow has...
Q: C program for the longest common array of 2 arrays. Use the: function void longestMutualSequence(in...
A: so we have to write a C program for the longest common array of 2 arrays. and we have to Use the: fu...
Q: Exercise 11.4. ¤ Write a function in Python that takes two inputs: • a list of points in R", • a pos...
A: Answer
Q: The example on page 190 of the textbook shows the restoring division of dividing 7 by 2. Redo the sa...
A: Dividend = 15Divisor = 2First the registers are initialized with corresponding values (Q = Dividend,...
Q: Isn't it true that different systems place disk folders at different track places on the disk for a ...
A: The answer is
Q: I Need to write a program based on the following Java program PercolationEstimation.java that uses b...
A: PercolationEstimation.java:- Solution is given below:-
Q: Tb=1; fc=10; t=0:Tb/100:1; c=sqrt(2/Tb)*sin(2*pi*fc*t);
A: The goal of these BASK commands is to imitate fourier series noise. The result is a curve with a pea...
Q: What is the difference between the technologies of "data mining" and "OLAP"?
A: SNO. Data Mining OLAP 1. It is used to predict the future. OLAP is used to analyze the past. 2. ...
Q: Cloud computing creates at least two challenges in terms of business security
A: Answer: In today's world what is actually want in the business is that we have to secure all your co...
Q: What do you understand by Reflection in Java programming language
A: What do you understand by Reflection in Java programming language
Q: Batch-function normalization's What settings should we tweak for batch normalization? What is the be...
A: Normalization of many batches Batch normalization is a method that is used in extremely neural netwo...
Q: Write a program that determines the real roots of a quadratic equation. To calculate the roots of th...
A: Given: given by: D = b ^ 2 - 4ac . If D > 0 the program displays message "The equation has two...
Q: hat is the origin of the file space hierarchy?
A: Task : Write down about file space hierarchy. Write down about its origin.
Q: 2. A Karnaugh map is nothing more than a special form of truth table, useful for reducing logic func...
A:
Q: Use R program as shown below then apply and construct a suitable graphical display of the generated ...
A: Answer I have done code and also I have attached code and code screenshot as well as output
Q: find the simplified circuit
A:
Q: The four cache replacement policies are explained in this chapter.
A: check further steps for the answer :
Q: How many times is Step 6 executed in the following algorithm? What is the time complexity of the alg...
A: An algorithm is a sequence of logical instructions used to arrive at the solution for a complex prob...
Q: What exactly does "open architectural design" imply?
A: Introduction: Architecture definitions. Some individuals believe that architecture is similar to por...
Q: Computer Science ( C# ) Create the Class1 class that contains private variable of integer type. Pub...
A: In main program create object of class Class1 type. Using the property assign and return values from...
Q: draw the simplified circuit
A: Answer:
Q: It is vital to comprehend how multiprocessor systems interact with one another in order to classify ...
A: Systems with several processors Multiprocessor systems are those that include many processors. Multi...
Q: Computer Science Establish the input, processing, and output of airline and hotel reservation credi...
A: Establish the input, processing, and output of airline and hotel reservation credit card transaction...
Q: You've been assigned by a primary/secondary or higher education school with creating a system for sc...
A: Introduction: Virtual memory is a piece of volatile memory that temporarily forms on the storage dev...
Q: For microprocessors and their accompanying systems, power supply and dissipation limits have become ...
A: A central processing unit (CPU) manages the many components of a microprocessor system, A common set...


Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- Java function to Find whether a given number is a power of 4 or not Example : powerOfFourOrNot(2) -> false powerOfFourOrNot(16) -> trueWithout using = operatorThe quadratic formula is used to solve a very specific type of equation, called aquadratic equation. These equations are usually written in the following form:ax2 + bx + c = 0The Quadratic Formula x = ( -b ± √( b^2 - 4ac ) ) / ( 2a ) Where a, b, and c are constants with a ≠ 0. (If a = 0, the equation is a linear equation.)The discriminant is the part of the formula in the square root. If the value of the discriminant is zero then the equation has a single real root. If the value of thediscriminant is positive then the equation has two real roots. If the value of thediscriminant is negative, then the equation has two complex roots.Write a program that finds the roots of the quadratic equation using the Quadratic Formula. Write a function named discriminant in the file, Disc.py, to calculate and return the discriminant of the formula. Let the main function call the discriminant function and then calculate the solution(s) of the equation. Do not calculate the solutions in the discriminant…
- 1. Evaluate !(1 && !(0 || 0)). (Answer True or False only) 2. The associativity rule of logical operators is ___Brute force equation solver this is python program. Numerous engineering and scientific applications require finding solutions to a set of equations. Ex: 8x + 7y = 38 and 3x - 5y = -1 have a solution x = 3, y = 2. Given integer coefficients of two linear equations with variables x and y, use brute force to find an integer solution for x and y in the range -10 to 10. Ex: If the input is: 8 7 38 3 -5 -1 Then the output is: 3 2 Use this brute force approach: For every value of x from -10 to 10 For every value of y from -10 to 10 Check if the current x and y satisfy both equations. If so, output the solution, and finish. Ex: If no solution is found, output: No solution You can assume the two equations have no more than one solution. Note: Elegant mathematical techniques exist to solve such linear equations. However, for other kinds of equations or situations, brute force can be handy. ''' Read in first equation, ax + by = c '''a = int(input())b = int(input())c = int(input()) ''' Read in…جد نتيجة التعبير التالي K-2; A=3; S-5 M-K>A C=.NOT.M P-A>K.OR.S-2.AND..NOT.C.OR.M
- When you borrow money to buy a house, a car, or for some other purpose, you repay the loan by making periodic payments over a certain period of time. Of course, the lending company will charge interest on the loan. Every periodic payment consists of the interest on the loan and the payment toward the principal amount. To be specific, suppose that you borrow $1,000 at an interest rate of 7.2% per year and the payments are monthly. Suppose that your monthly payment is $25. Now, the interest is 7.2% per year and the payments are monthly, so the interest rate per month is 7.2/12 = 0.6%. The first months interest on $1,000 is 1000 0.006 = 6. Because the payment is $25 and the interest for the first month is $6, the payment toward the principal amount is 25 6 = 19. This means after making the first payment, the loan amount is 1,000 19 = 981. For the second payment, the interest is calculated on $981. So the interest for the second month is 981 0.006 = 5.886, that is, approximately $5.89. This implies that the payment toward the principal is 25 5.89 = 19.11 and the remaining balance after the second payment is 981 19.11 = 961.89. This process is repeated until the loan is paid. Write a program that accepts as input the loan amount, the interest rate per year, and the monthly payment. (Enter the interest rate as a percentage. For example, if the interest rate is 7.2% per year, then enter 7.2.) The program then outputs the number of months it would take to repay the loan. (Note that if the monthly payment is less than the first months interest, then after each payment, the loan amount will increase. In this case, the program must warn the borrower that the monthly payment is too low, and with this monthly payment, the loan amount could not be repaid.)[ I C ) ] » (z F ) Given Statement: 2. Truth Values: Main Operator: Based on this truth-functional calculation, the given compound statement is IIThe execution of SUB AL, BL is performed by а. both EU and BIU O b. neither EU nor BIU Ос. EU O d. BIU











