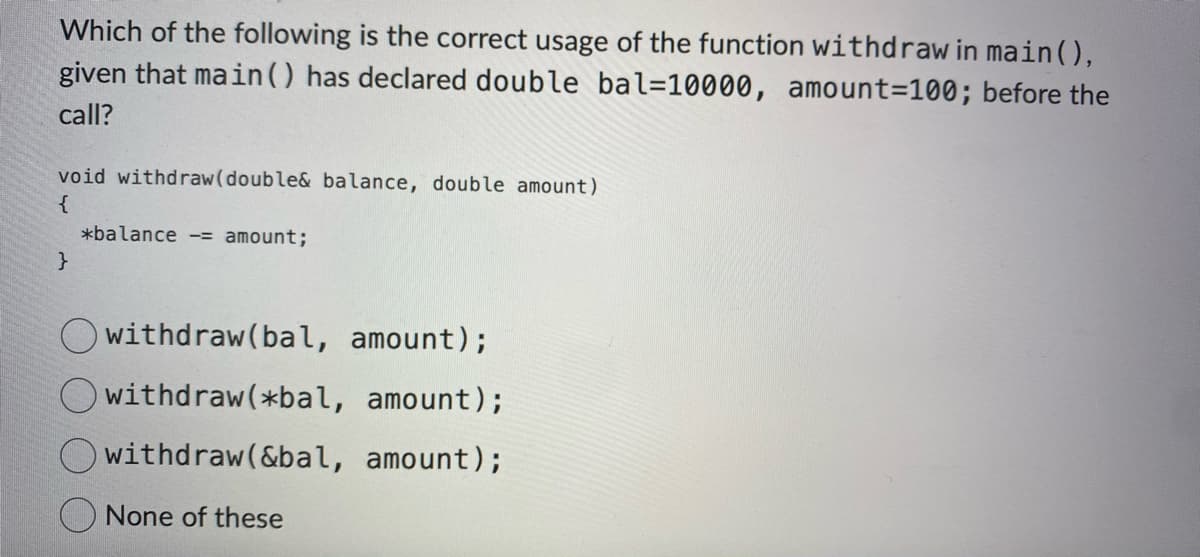
Which of the following is the correct usage of the function withdraw in main(), given that main () has declared double bal=10000, amount=100; before the call? void withdraw(double& balance, double amount) { } *balance = amount;
Q: For the following MATLAB code, It is supposed to perform the convolution of two continuous time…
A: The convolution operation is essential for integrating two signals into a single resultant signal in…
Q: So on the iphone, what does notification grouping look like? What does show privews look like? What…
A: When many notifications from the same app or discussion are arranged into a neat stack or bundle for…
Q: Describe the purpose and usage of exception handling in a programming language of your choice.
A: Exception handling is a process of responding to unexcepted or unwanted events when computer program…
Q: Explain the principles of continuous integration and continuous deployment (CI/CD) in the context of…
A: Continuous Integration (CI) and Continuous Deployment (CD) have become indispensable components of…
Q: should I connect a DRV8833 Dual Motor Driver Module to an ESP32 Dev board
A: In this question you asked guidance to connect a DRV8833 Dual Motor Driver Module to an ESP32 Dev…
Q: Explore the security features provided by protocols such as SSL/TLS in ensuring secure communication…
A: In the vast expanse of the internet, security stands as a paramount concern, and protocols like…
Q: Elaborate on the purpose and implementation of VLANs (Virtual Local Area Networks) in network…
A: Virtual Local Area Networks (VLANs) play a role in network architecture as they allow for the…
Q: Create a "Branflake" program that will accept two integers in the form of a string "x+y", add the…
A: I have provided PYTHON CODE along CODE SCREENSHOT and OUTPUT SCREENSHOT....
Q: Elaborate on the security implications of SSL/TLS protocols and how they contribute to secure…
A: Secure Sockets Layer (SSL) and Transport Layer Security (TLS) are protocols created to enable…
Q: Is your language regular? If so, give a regular expression for the language. If not, demonstrate…
A: The Pumping Lemma is a powerful tool for proving that a language is not regular. The lemma states…
Q: The table VideoVisitFact has a single primary key column of VideoVisitKey. The column is numeric.…
A: The table VideoVisitFact has a single primary key column of VideoVisitKey. We need to find query…
Q: Discuss the microkernel architecture and its application in modern operating systems.
A: Answer:Introduction:1) Microkernel is one of the designing approach in Operating system.2) Here each…
Q: Using WebGL (HTML & JavaScript), how do you create a program that will produce an approximated and…
A: <!DOCTYPE html><html lang="en"><head> <meta charset="UTF-8"> <meta…
Q: Beatrice wants to implement cloud computing for cost savings. Which of the following is a factor…
A: The delivery of computing resources over the internet is referred as cloud computing. Some of the…
Q: consider a data base system applying replication on logs, assuming each transaction on average…
A: To calculate the time overhead for replication in a database system, we need to consider the time it…
Q: Explore the concept of I2C (Inter-Integrated Circuit) and SPI (Serial Peripheral Interface)…
A: 1) Communication protocols in the context of microcontrollers refer to a set of rules and…
Q: Discuss the security aspects of network protocols. How does Secure Socket Layer (SSL) contribute to…
A: Network protocols can be defined in such a way that they are the essential building blocks of net…
Q: Discuss the purpose and functionality of ARP (Address Resolution Protocol) in computer networks.
A: The Address Resolution Protocol (ARP) plays a crucial role in computer networks, in facilitating…
Q: (a) Construct a finite state automaton which recognizes strings over {0, 1} that begins with 101 and…
A: To construct a finite state automaton we first need to define states and transitions.
Q: A company in the Home Delivery domain "On-Time Safely" requested the submission of several software…
A: Note: According to bartleby rules and guidelines we can only answer first 3 subquestions, please…
Q: So what does "Email history and attatchments" mean in google drive? What specifically and exactly…
A: Google Drive is a cloud-based storage service by Google, offering users a secure platform to store,…
Q: So right now in my iphone, I have my notifications display set to "list" and have notification…
A: When many notifications from the same app or discussion are arranged into a neat stack or bundle for…
Q: nstructions Write a program to test various operations of the class doublyLinkedList. Your program…
A: A doubly linked list is a data structure that consists of nodes, each containing a data element and…
Q: Explain the OSI model and its seven layers, detailing the functions and protocols associated with…
A: The OSI (Open Systems Interconnection) model is a framework that standardizes the functions of a…
Q: Discuss the trade-offs involved in selecting between microcontrollers and microprocessors for a…
A: When it comes to embedded systems, making a choice between microcontrollers and microprocessors for…
Q: Describe the function of NAT (Network Address Translation) in the context of network architecture…
A: A key element of contemporary network architectures is network address translation (NAT), which…
Q: Describe the function of GPIO (General Purpose Input/Output) pins on a microcontroller.
A: GPIO (General Purpose Input/Output) pins play a role in connecting a microcontroller to…
Q: Discuss the importance of memory management in embedded systems and how it is typically handled in…
A: Memory management in embedded systems involves the strategic allocation, utilization, and…
Q: Q1) Filtering Files Assume the information of all the TAs for the ECE department is stored in a file…
A: In this question we have to write a C++ code for the student file filtering to remove/alter alum…
Q: Explore the concept of embedded systems and their applications in various industries.
A: Embedded systems, the silent architects of modern technology, are discreet yet powerful computing…
Q: brief explanation with examples of the following points: 1.random processes 1.1 temporal…
A: We have to explain the given following terms in a short explanation:1. random processes1.1 temporal…
Q: 4) In Adobe Flash what are the key differences between ActionScript 2.0 and ActionScript 3.0 in…
A: Adobe flash which was originally among the most prominent web platforms comprising animation, web…
Q: Identify two challenges of using images in multimedia documents and explain how each challenge is…
A: An image is a representation in visual form, usually in two dimensions, of an object, scene, idea,…
Q: Using Java and the pictures create a program that has tabs for food, drinks, dessert, receipt,…
A: Creating a full Java GUI application for a food ordering system with tabs for different sections…
Q: Delve into the principles of design patterns and elucidate how they contribute to scalable and…
A: Design patterns are a set of solutions that can be used repeatedly to solve problems encountered…
Q: 3. Suppose we have four training examples under the two-category case, i.e. D* = {(x₁,w₁) |1 ≤ i ≤…
A: In this scenario, tasked with employing gradient descent techniques to minimize a criterion function…
Q: Discuss the features and benefits of using Field-Programmable Gate Arrays (FPGAs) in comparison to…
A: When it comes to system design both Field Programmable Gate Arrays (FPGAs) and microcontrollers play…
Q: We are looking for a programming language that is strictly typed, but also allows users for partial…
A: In this question we have to understand about the programming language that is strictly types, but…
Q: What is the significance of exception handling in software development? Provide examples of…
A: Exception handling in software development is a important component for creating robust and…
Q: 7. For each of the following relations on the set of all real numbers, solve all of the subparts as…
A: When examining relations on the set of real numbers, certain properties like reflexivity, symmetry,…
Q: Explain the purpose and implementation of pulse-width modulation (PWM) in microcontroller-based…
A: Pulse width modulation (PWM) is a technique extensively used in systems driven by microcontrollers…
Q: Describe the function of EEPROM (Electrically Erasable Programmable Read-Only Memory) in…
A: EEPROM, also known as Electrically Erasable Programmable Read Memory, is a type of memory commonly…
Q: Create a project in Eclipse® named ColourScheme. Include two classes: Blocks & BlocksViewer. In a…
A: In this question we have to write a Java code named colourScheme which displays colours in blocks in…
Q: Explain the concept of dependency injection and its advantages in software architecture.
A: Dependency injection (DI) is a software architecture design pattern that focuses on managing the…
Q: 2.Assume list1 is a list of integers. Write a statement that uses a list comprehension to create a…
A: Initialize list1 with a list of integers.Use a listing comprehension to iterate over each element x…
Q: Describe the role of ICMP (Internet Control Message Protocol) in network troubleshooting.
A: ICMP, also known as Internet Control Message Protocol, is a part of the Internet Protocol (IP)…
Q: The dynamics of academic performance at XYZ Primary School were analyzed by considering the opinions…
A: Here I am going to use MS PowerPoint 365 to ease the process. I have developed three Graphs using…
Q: In this task, a skip list data structure should be implemented. You can follow the following…
A: The question does not specify any particular programming language. We have done the solution using…
Q: Explore the concept of subnetting in IP addressing, and provide a step-by-step guide on how to…
A: Subnetting is a technique used in IP networking to divide a larger network into smaller, more…
Q: Elaborate on the security mechanisms provided by SSL/TLS protocols and their role in ensuring secure…
A: Secure Sockets Layer (SSL) and Transport Layer Security (TLS) are protocols that supply…
Trending now
This is a popular solution!
Step by step
Solved in 5 steps with 1 images

- Create a function employeeSalary() in such a way that it should accept employee name, and its salary and display both. If the salary is missing in the function call assign default value 40,000 to salary. Output: Employee salary is: 40,000 Employee Ben salary is: 40,000The food pantry provides its volunteers with keys to unlock doors and a Food Pantry vest to let customers know they work there. There are a limited amount of keys and vests, so volunteers need to check them out of the office.Complete the program by creating a CheckoutEquipment function that takes in the number of keys and vests currently available at the office. If there are enough keys and vests, the function should reduce the number of keys and vests by 1 and return true. Otherwise, the number of keys and vests will stay the same, and the function will return false. Take note that the number of keys and vests will be defined in the main function and the CheckoutEquipment function should modify the values of those variables declared in main. #include <iostream> int main() { int keys = 10; int vests = 10; bool checked_out = CheckoutEquipment(keys, vests); if (checked_out) { std::cout << "Successfully checked out.\n"; } else { std::cout << "Not…Please enumerate all of the situations when invoking inline functions will not get the expected results.
- Consider the definition of the function main. int main() { double rate, hours, amount; . . . } Each of the functions described must have the appropriate parameters to access these variables. Write the following definitions: a. Write the definition of the function getHoursRate that prompts the user to input the hours worked and rate per hour to initialize the variables hours and rate of the function main. b. Write the definition of the value-returning function payCheck that calculates and returns the amount to be paid to an employee based on the hours worked and rate per hour. The hours worked and rate per hour are stored in the variables hours and rate, respectively, of the function main. The formula for calculating the amount to be paid is as follows: For the first 40 hours, the rate is the given rate; for hours over 40, the rate is 1.5 times the given rate. c. Write the definition of the function printCheck that prints the hours worked, rate per hour, and the…What is a function called when its return value is always the same for the same arguments? 1. Curried function 2. Overloaded function 3. Pure function 4. Polymorphic function 5. Strict functionCreate a function employeeSalary() in such a way that it should accept employee name, and its salary and display both. If the salary is missing in the function call assign default value 40,000 to salary. Output: Employee salary is: 40,000 Employee Ben salary is: 40,000 PLEASE SHOW IT IN PYTHON PROGRAM
- Explain how invoking inline functions differs from calling standard functions in the background.Write a type script function that takes in a student number, programme registered for, balance, and cell contact number as an optional parameter. The function should then display the fields to the console if the balance is less that N$5000.Please elaborate on the benefits of user-defined functions over built-in ones.
- Which statement below is true about a function: may have no parameters must always have a return statement must have at least one parameter its arguments always appear within bracketsDescribe all the situations in which invoking inline functions will not provide the expected outcomes.Consider the definition of the function main:int main(){int x, y;char z;double rate, hours;double amount;...} The variables x, y, z, rate, and hours referred to in items a through f below are the variables of the function main. Each of the functions described must have the appropriate parameters to access these variables. Write the following definitions:a. Write the definition of the function initialize that initializes x and y to 0 and z to the blank character.b. Write the definition of the function getHoursRate that prompts the user to input the hours worked and rate per hour to initialize the variables hours and rate of the function main.c. Write the definition of the value-returning function payCheck that calculates and returns the amount to be paid to an employee based on the hours worked and rate per hour. The hours worked and rate per hour are stored in the variables hours and rate, respectively, of the function main. The formula for calculating the amount to be paid is as…

