instruction- This file should have multiple lines, each line has first name, last name followed by multiple integers “data.txt” file Samantha Johns 43, 32,99, 79, 85 Michael Smith 98, 84, 70, 100, 76, 81 John Michael 82,92, 92 Mary Hernandez 88, 91, 92, 79, 78 George Johnson 92,93,75 Sara Anderson 83,74. Susan John 78, 84,65, 71,81 Mark Smith 69, 67,59,62
instruction- This file should have multiple lines, each line has first name, last name followed by multiple integers “data.txt” file Samantha Johns 43, 32,99, 79, 85 Michael Smith 98, 84, 70, 100, 76, 81 John Michael 82,92, 92 Mary Hernandez 88, 91, 92, 79, 78 George Johnson 92,93,75 Sara Anderson 83,74. Susan John 78, 84,65, 71,81 Mark Smith 69, 67,59,62
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter8: Arrays And Strings
Section: Chapter Questions
Problem 6PE
Related questions
Question
instruction- This file should have multiple lines, each line has first name, last name followed by multiple integers
“data.txt” file
Samantha Johns 43, 32,99, 79, 85
Michael Smith 98, 84, 70, 100, 76, 81
John Michael 82,92, 92
Mary Hernandez 88, 91, 92, 79, 78
George Johnson 92,93,75
Sara Anderson 83,74.
Susan John 78, 84,65, 71,81
Mark Smith 69, 67,59,62
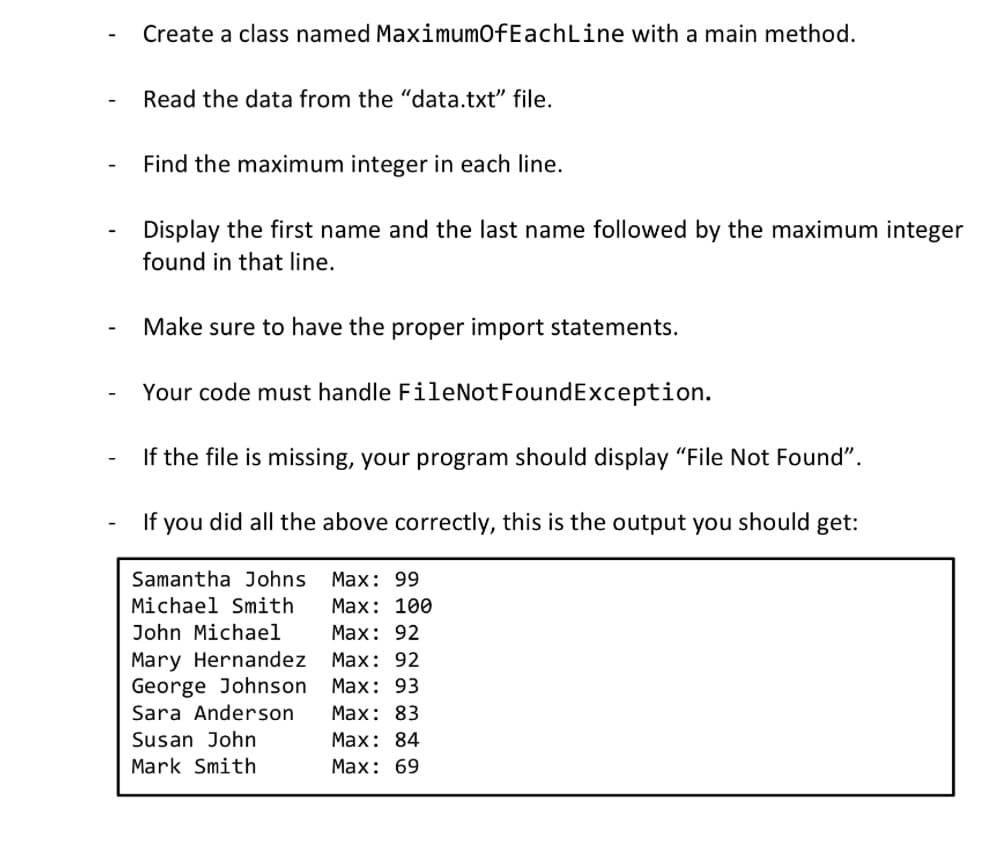
Transcribed Image Text:Create a class named MaximumOfEachLine with a main method.
Read the data from the "data.txt" file.
Find the maximum integer in each line.
Display the first name and the last name followed by the maximum integer
found in that line.
Make sure to have the proper import statements.
Your code must handle FileNotFoundException.
If the file is missing, your program should display "File Not Found".
If you did all the above correctly, this is the output you should get:
Samantha Johns Max: 99
Michael Smith
Max: 100
Max: 92
Max: 92
Max: 93
Max: 83
Max: 84
Max: 69
John Michael
Mary Hernandez
George Johnson
Sara Anderson
Susan John
Mark Smith
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT