I need your help! I'm trying to form a spirit bomb and I need all the power I can get! But in order to get power, I need as many powers of 2 as I can get! I can't seem to tell which of the values are powers of 2 though, but that's why you're here!
I need your help! I'm trying to form a spirit bomb and I need all the power I can get! But in order to get power, I need as many powers of 2 as I can get! I can't seem to tell which of the values are powers of 2 though, but that's why you're here!
Chapter8: Arrays
Section: Chapter Questions
Problem 9PE
Related questions
Question
code in c

Transcribed Image Text:I need your help! I'm trying to form a spirit bomb and I need all the
power I can get! But in order to get power, I need as many powers of
2 as I can get! I can't seem to tell which of the values are powers of 2
though, but that's why you're here!
Inputs
1. Size of the integer array.
2. Elements of the integer array.
Sample Output
Enter the size: 5
Enter the elements: 1 2 4 9 16
Powers of 2 = 16 4 2 1
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 1 images

Follow-up Questions
Read through expert solutions to related follow-up questions below.
Follow-up Question
The code in c should match this outputs
Transcribed Image Text:F1
ach
Gigantone, Rochell
kocnene JoyGe
Test Cases
Executions
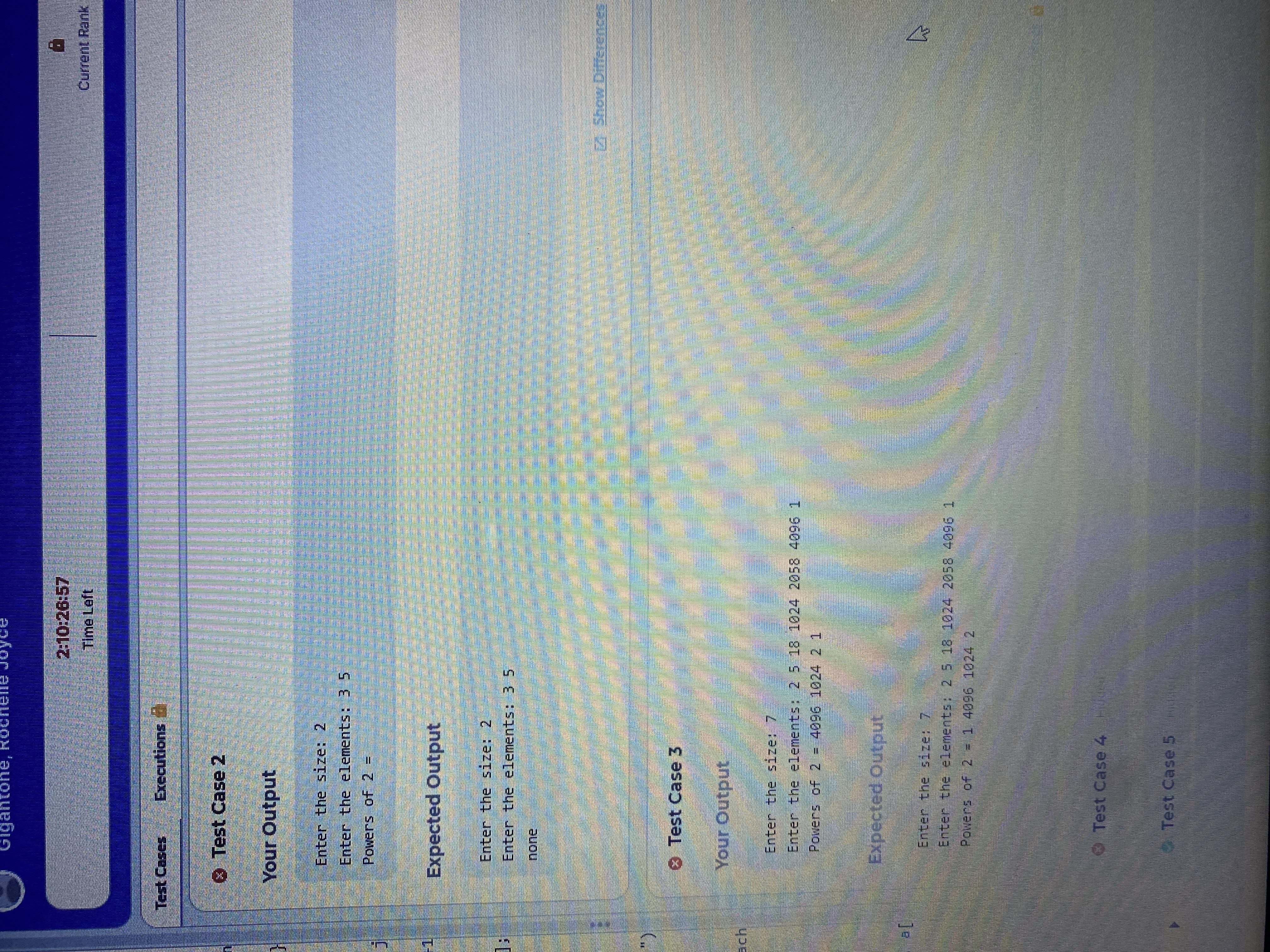
Test Case 2
Your Output
Enter the size: 2
Enter the elements: 35
Powers of 2 =
Expected Output
Enter the size: 2
Enter the elements: 3 5
none
Test Case 3
Your Output
Enter the size: 7
Enter the elements: 2 5 18 1024 2058 4096 1
Powers of 2 = 4096 1024 2 1
Expected Output
2:10:26:57
Time Left
Enter the size: 7
Enter the elements: 2 5 18 1024 2058 4096 1
Powers of 2 = 1 4096 1024 2
Test Case 4
Test Case 5
1
# 5
Current Rank
2 Show Differences
4
Solution
Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage