1- Given R0, RI, R2, and R3 followed by the indicated base; i- Convert each value into its corresponding 9 bit binary value, the most significant bit is used as the sign bit, separate the sign bit with a comma, for example; 0,10100000 (RO)8 = 165 (RO)2= Use the 9 least significant bits, discard the extra bits. (RI)16 - FSF (RI)2- (R2)16 = F81 (R2)2= (R3)7 152 (R3)2- (Separte the sign from the other bits with a comma, for example; 110011000 is written as; 1,10011000) ii- Evaluate; R4 - RO + RI. (consider negative numbers to be already given in 2's complement) bitk hbittbitir4bitbi2birlhio RO RI R4
1- Given R0, RI, R2, and R3 followed by the indicated base; i- Convert each value into its corresponding 9 bit binary value, the most significant bit is used as the sign bit, separate the sign bit with a comma, for example; 0,10100000 (RO)8 = 165 (RO)2= Use the 9 least significant bits, discard the extra bits. (RI)16 - FSF (RI)2- (R2)16 = F81 (R2)2= (R3)7 152 (R3)2- (Separte the sign from the other bits with a comma, for example; 110011000 is written as; 1,10011000) ii- Evaluate; R4 - RO + RI. (consider negative numbers to be already given in 2's complement) bitk hbittbitir4bitbi2birlhio RO RI R4
Chapter8: Data And Network Communication Technology
Section: Chapter Questions
Problem 41VE
Related questions
Question

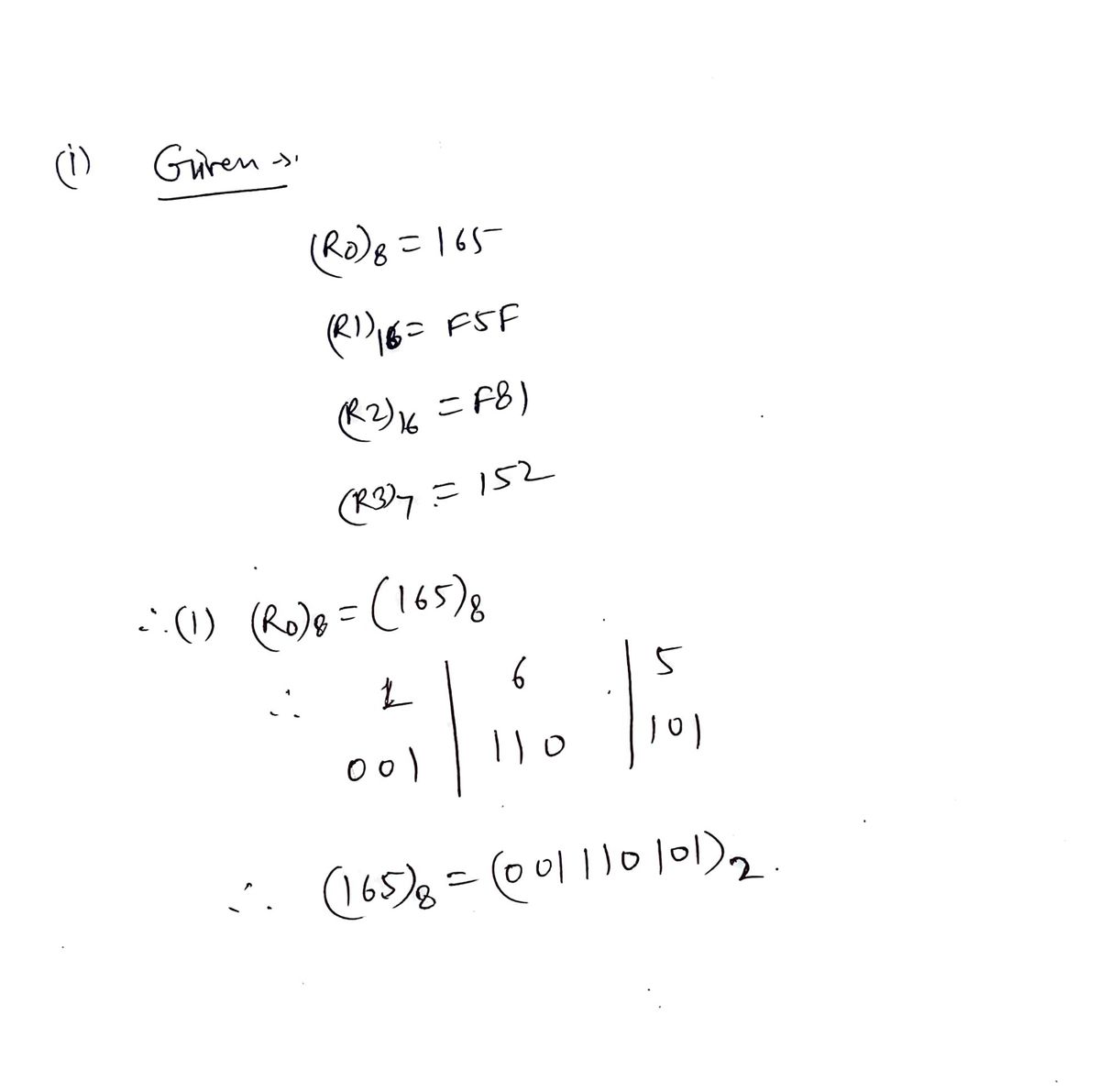
Transcribed Image Text:1- Given RO, R1, R2, and R3 followed by the indicated base;
i- Convert each value into its corresponding 9 bit binary value, the most significant bit is used as the sign bit, separate the sign bit with a comma, for example; 0,10100000
(RO)8 =
165
(RO)2=
Use the 9 least significant bits, discard the extra bits.
(RI)16 - FSF
(RI)2=
(R2)16 = F81
(R2)2=
(R3)7
152
(R3)2-
%3D
(Separte the sign from the other bits with a comma, for example; 110011000 is written as; 1,10011000)
ii- Evaluate; R4 - RO + RI. (consider negative numbers to be already given in 2's complement)
bit8 bit 7bitóbitit4bit3bit2bitl bito
RO
RI
R4
Expert Solution
Step 1
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 4 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning